What Is An Audit Trail And What Is Its Purpose – It is a general principle that well-managed audit trails are key indicators of good internal business controls. Audit trails have moved from manual to automated electronic logs that make this historical information more accurate, easier to access and more useful. Successful audit trails require a top-down commitment from upper management, the departments involved and IT staff. The sooner an abnormal change or addition to information is “red flagged,” the better the response to mitigate negative impacts such as cyber threats, security breaches, data corruption or information misuse.
This article defines an audit trail, what to include, the importance of tracking this information, and how to best manage audit trail data. We then demonstrate examples of audit trails you might find in your business systems.
What Is An Audit Trail And What Is Its Purpose

Are secure records that catalog events or procedures to provide supporting documentation. They are used to authenticate security and operational actions, mitigate challenges, or provide evidence of compliance and operational integrity.
About Audit Trail
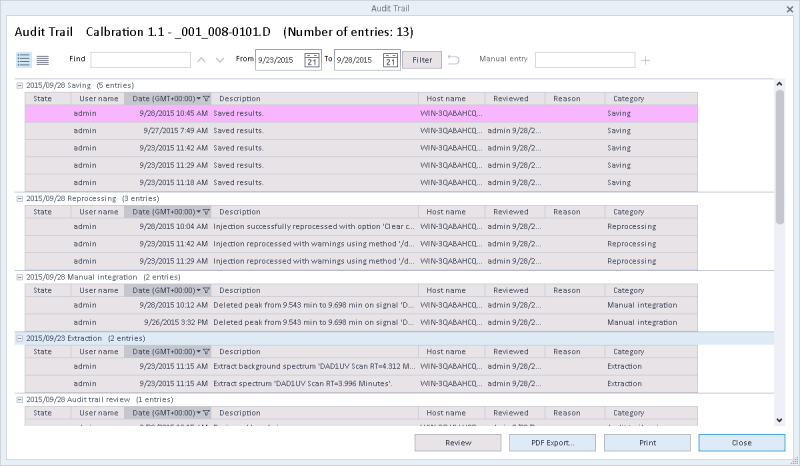
Numerous industries use versions of an audit trail to provide a historical overview of progress based on a series of events. Whether recording design changes to a product, tracking financial transactions for an e-commerce site, communications transactions, healthcare operations, or legitimizing the outcome of an election, an audit trail validates actions and results. Audit trail records contain details such as the date, time, and user information associated with the transaction. As a result, audit trails can identify areas of non-compliance by providing information for audit investigations.
IT plays an important role in the overall process of industry or regulatory specific audit logs and trails. However, the department itself has a unique and dense logging process that continuously monitors the numerous and varied activities of users, systems and applications to prevent misuse, hacking or corruption of information. IT professionals use this validation system as an essential tool to analyze the operation and technical controls of computer systems. An audit trail is used to validate and monitor activities and provides a tool to maintain information and system integrity.
Can mean different things. Systems can also maintain different types of audit trails and logs for different purposes. Logging usually deals with program-level events, such as administrative actions and abnormal related events that technical personnel use to detect software problems. This identifies system problems before they become significant enough to cause damage, such as system failures or malfunctions, which can hinder productivity. In contrast, auditing usually refers to user-level transactions, such as a change to a financial record made by “Joe Smith” at “10:00 AM” on “December 21, 2016.”
Most solutions have two separate sets of logs that are maintained simultaneously, including cloud platforms. For example, Google’s cloud solution maintains an administrative activity log that tracks API calls and configuration changes, and a data access log that records updates or changes to user-provided data.
Audit Trail & History
An audit trail provides basic information to trace back through the entire trail of events to the origin, usually the original creation of the record. This may include user activity, data access, login attempts, administrator activity, or automated system activity. Audit records contain elements defined by the company, including:
Some audit trails look more closely at actions within certain applications to record more than just starting a system or application. These log files can track items such as specific changes to a database or information contained therein, and can also detect inappropriate web surfing or email usage. Many IT departments have more than one audit trail that can be system, application or event defined. By drawing attention to abnormal activities or uses that are considered ‘extraordinary’, an investigation can be initiated. An accurate and well-defined audit trail provides the evidence to find answers and solve problems.
The Sarbanes-Oxley Act requires applicable US companies to keep their logs for a minimum of seven years and maintain the audit trail for the life of the data if possible. Keeping logs is useful for reporting and troubleshooting in the future.

IT audit trails are designed to address numerous activities that are part of an event or series of events that can be examined to find areas of concern. Problem activities include security breaches by hackers, internal or external authentication issues, unauthorized use, unusual activity levels, or system failures. Records include the automated events scheduled through the operating system (OS), network access, application events, and manual activities of the different users. Normal activities may include application access and system authentication.
Audit Trail In Salesforce: How To Setup And Use Audit Trail
However, when unusual or abnormal usage is detected, such as large-scale data changes, application errors or unauthorized access, the system provides means to follow a trail to identify and then fix the problem. Other unusual activities that may occur include inconsistent user activity patterns, attempts to circumvent systems or protocols, large-scale changes in information, and unusual Internet activity.
Each company’s frequency will vary, but the National Institute of Standards and Technology (NIST) suggests conducting periodic audits of assessment logs as often as necessary depending on their industry and security needs.
In some cases, regulations may dictate a specific time frame in which logs must be reviewed. For example, if you have an audit committee involved in your company, they can define a regularly scheduled review, such as semi-annually or annually.
The need to support compliance, security and operations is reflected in most (if not all) industries. The laws that both mandate and regulate the use of electronic documents make audit documents an important element in defending against security breaches, supporting compliance reporting, and ultimately passing numerous types of internal and external audits. Industries that have facilities to track the integrity of information include government agencies and universities that maintain sensitive, confidential information, and any company that uses electronic documents that contain confidential information. Every industry, whether tracking data or transactions, will benefit from maintaining accurate audit logs.
What Are Audit Trails & Why You Need Them In Cd
To that end, there is a growing need for businesses, as well as government and educational institutions, to maintain and provide accurate and verifiable information. If an organization uses a database management system to manage records, chances are they are recording audit trails.
The audit trail provides a “baseline” for analysis or an audit when initiating an investigation. The purpose or importance of an audit trail takes many forms depending on the organization: A company may use the audit trail for reconciliation, historical reporting, future budget planning, tax or other audit compliance, crime investigation, and/or risk management.
Irit Gillath is VP Marketing at syslink, a provider of SAP management, monitoring and analytics solutions. “SAP systems can store credit card information, HR data, financial information or even health data, among a host of other highly secure data,” she says. “It is important for our customers to keep records of changes and activities taking place in the SAP system to prepare for audits, ensure security and compliance, and identify the sources of problems.”

Audit trails are managed by IT department employees. Every user who touches the electronic file is included in the audit trail. This user can be a human or electronic system that automatically updates and changes.
Audit Trail And Usage Tracking Dashboard
The ability to track documents back to their origins provides numerous benefits, including transparency and defense of documents for compliance, integrity and accuracy of documents, system protection against misuse or damage, and security of sensitive or vital information. These are achieved through these four areas:
Since most industries today fall under various regulatory statutes, both in the US and internationally, these entities, especially those that maintain electronic records, must maintain a robust and accurate audit log and trail system. The IT department plays a critical role in the maintenance, security, availability and integrity of records to provide auditable information to defend industry compliance.
Regulatory statutes such as the Health Insurance Portability Act (HIPAA), Sarbanes-Oxley (SOX), and Gramm-Leach-Bliley Act (GLBA) impose requirements not only on the proper maintenance of electronic records, but also on mechanisms for proper compliance and audit . . Most industries rely on the support of IT services to maintain their electronic records to control record keeping, provide appropriate and protected user access, and provide strong privacy controls that they can track and restrict. The sectors most in need of a robust audit trail policy include financial services, communications, e-commerce sites, universities and healthcare services and providers.
According to Elizabeth Sinclair, Verticals Marketing Manager for BarTender at Seagull Scientific, “Our pharmaceutical and medical device manufacturing customers tend to be advanced technology users. The FDA’s 21 CFR Part 11 rule requires them to maintain time-stamped audit trails of all packaging and supply chain labeling events: what changes were made to a template, who changed or printed a label, what printers the job was sent to , or the user was allowed to perform a system action or access was denied, and in some cases they are required to capture an image of the label – and they use our software to capture and catalog this information.
What Is An Audit Trail Report? Definition And Examples
Healthcare organizations are required to adhere to strict security measures and remain compliant with HIPAA guidelines, which means audit trails and logs are extremely necessary to operate accurately
What is an audit committee and what are its responsibilities, what is a sukkah and what is its purpose, life and its purpose, what is the purpose of an audit report, what is hipaa and what is its purpose, what is the purpose of an audit, what is an audit trail and what is its purpose, purpose of an audit, audit trail purpose, what is an ercp and what is its purpose, what is osha and its purpose, what is the purpose of an internal audit